For actors, musicians, athletes, internet personalities, and other public figures, the threat model isn’t hiding behind an alias — your real name is in IMDb, news archives, court filings, fan wikis, and scraped social. The question is what those public records connect to that you didn’t intend to publish: home address, family members, business filings, leaked credentials, old handles you forgot about.
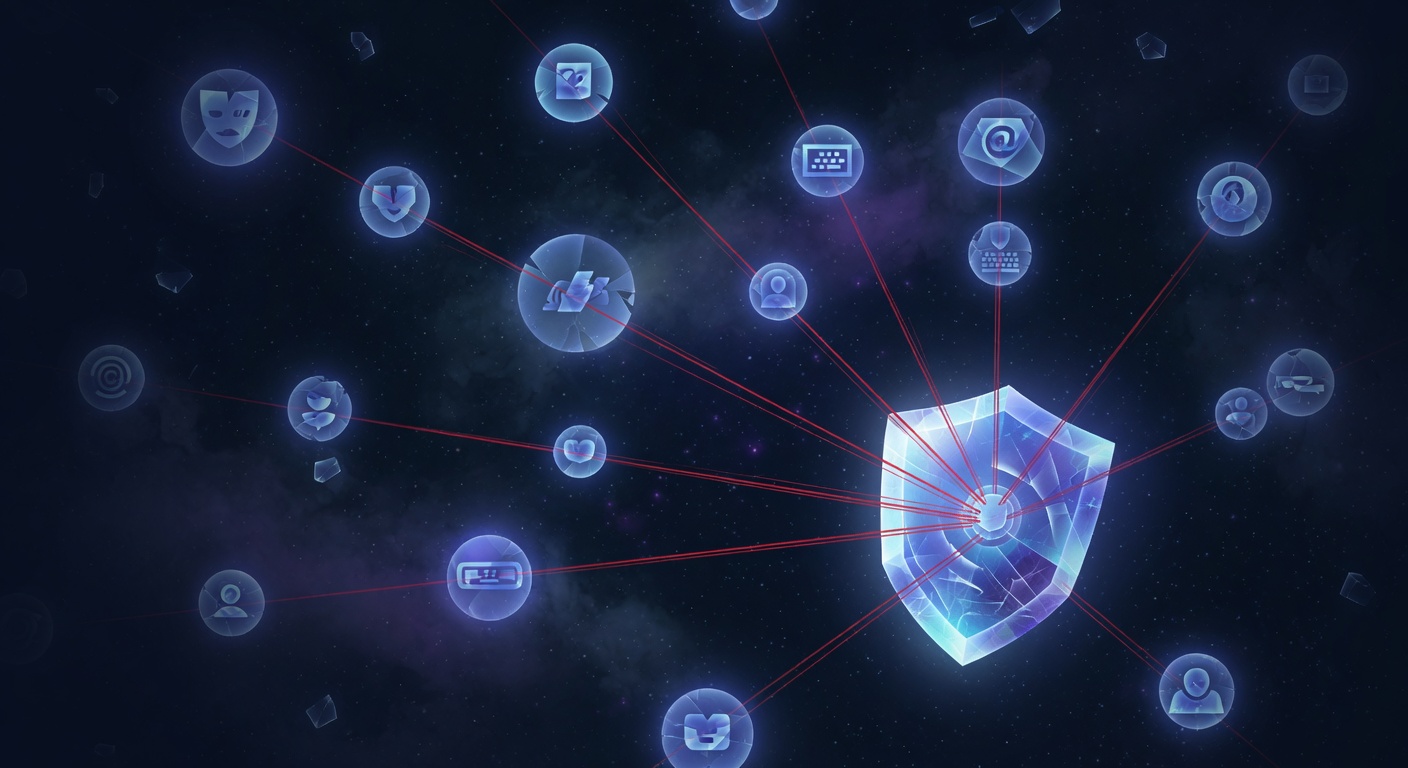
DoxxScan™ runs the same OSINT chain a stalker, tabloid researcher, or obsessed fan would — in reverse — so you see what they would find before they find it.

Public figures get profiled by people with time, motivation, and patience. The chains they build aren’t hypothetical — they’re published every week on tabloids, fan forums, and increasingly automated OSINT tools.
Real-name searches in property records, court filings, and family-tree sites chain to your home address, your relatives, and where your kids go to school.
Reporters and stringers run real-name lookups against scraped social, payment apps, dating apps, and breach data. The story usually starts with one public link they pulled off your IMDb entry.
Old handles, alt accounts, and gym check-ins from a decade ago chain to a live-tracking profile. Fan-wiki collaboration accelerates this.
The forgotten Tumblr / LiveJournal / gaming handle from before you were famous — and the breach data attached to it — is the most common re-identification vector we see.
Your team’s real names link to their public records, which link back to you. Personal assistants, security drivers, and family members are often the weakest chain in the graph.
15B+ indexed records means the password you used in 2014 is probably tied to your real name today. Combo lists weaponize this in seconds.
Most "breach checkers" only run one direction: you give them a handle, they tell you if it leaked. We do that too — and we run the inverse. Give us a real name, and we surface the handles, leaked records, and exposed PII it chains to.
Both queries feed the same engine. Findings on one side automatically chain back to the other so a single scan reveals the full graph — not a half-picture.
Most public figures start with the free scan to see the size of the problem, then move to white-glove monitoring once they see it themselves.
Scan by real name or by handle. Get your doxx-risk score, your full identity-chain map, breach matches, and an AI-generated remediation plan in under five seconds. Activate Warden from $4.17/mo (annual) for continuous monitoring — or Warden Plus from $8.25/mo (annual) for the full analyst Concierge.
Manual analyst-led identity defense for high-visibility public figures and their families & staff. Continuous monitoring, real-name takedown requests, data-broker opt-outs, dark-web watch, and direct response to active doxxing events. Pricing scales with coverage scope.
Why us. GalaxyWarden was built by an offensive-security practitioner — the same skill set the people running these chains use against you. We index 15B+ breach records, monitor 100+ platforms, and partner with healthcare-executive protection programs after the December 2024 incidents made this a board-level problem. If your name is on a magazine, a marquee, or a verified profile, we’ve almost certainly already mapped what it links to.